 |
 |
Cyber attack infects 550,000 of Apple's 'virus free' machines - UK and U.S. worst hit
|
 |
|
 |
|
Grizzled Veteran
Join Date: Aug 2007
Location: U.K.
Status:
Offline
|
|
|
(
Last edited by MacNNUK; Apr 7, 2012 at 03:16 PM.
)
|
|
iMac Intel Core i5, 2.5GHz, 4GB RAM, 500GB 21.5" Monitor 10.8.3.
iMac 17" 2.0ghz Intel Core 2 Duo w 3gb memory (White one) 10.6.8.
Internal 500gb / 8x external HDD's 250GB - 3TB (4x Time Machine)
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
I'd call it bullsh!t.
Yet another anti-virus vendor that attention-whores to get his product / name out.
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
More detailed info:
Threat Description: Trojan-Downloader:OSX/Flashback.I
If you have any of the following installed, the trojan will stop and delete itself.
/Applications/Microsoft Word.app
/Applications/Microsoft Office 2008
/Applications/Microsoft Office 2011
/Applications/Skype.app
/Library/Little Snitch
/Developer/Applications/Xcode.app/Contents/MacOS/Xcode
/Applications/VirusBarrier X6.app
/Applications/iAntiVirus/iAntiVirus.app
/Applications/avast!.app
/Applications/ClamXav.app
/Applications/HTTPScoop.app
/Applications/Packet Peeper.app
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Grizzled Veteran
Join Date: Aug 2007
Location: U.K.
Status:
Offline
|
|
|
(
Last edited by MacNNUK; Apr 7, 2012 at 03:16 PM.
)
|
|
iMac Intel Core i5, 2.5GHz, 4GB RAM, 500GB 21.5" Monitor 10.8.3.
iMac 17" 2.0ghz Intel Core 2 Duo w 3gb memory (White one) 10.6.8.
Internal 500gb / 8x external HDD's 250GB - 3TB (4x Time Machine)
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Aug 2001
Location: Nobletucky
Status:
Offline
|
|
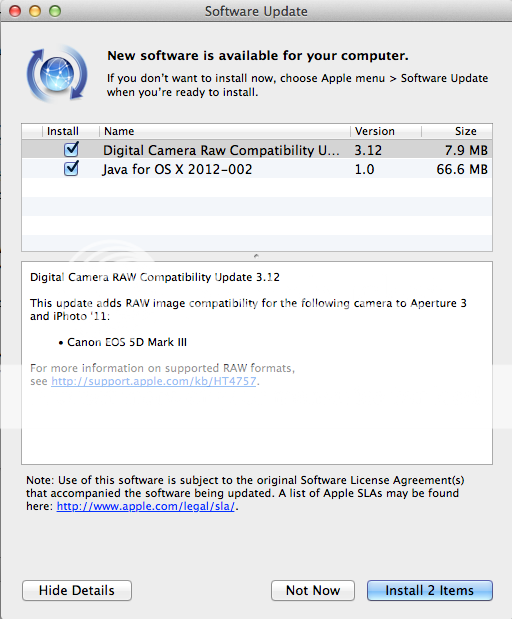
Exploits a hole in Java. Only IF you have Java installed. Run Software Update and install the Java fix. Done.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
That's why I doubt the 550,000 exploited Macs number.
* You need to have Java installed
* You need to be surfing to a site distributing that trojan
* You can't have any of the apps listed above installed (if you enter your admin credentials, Word, Office 2008/2011 and Skype are of no "protection")
Somehow seems like quite a bit of coincidences that need to come together.
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Oct 2000
Location: Los Angeles
Status:
Offline
|
|
Why would they write it to uninstall if it finds Word installed? What sense does that make from the trojan author's perspective?
Either way, this type of exploit should not have been possible. It's hard to believe that Java is still such a high security risk after all this time. You'd think it would be mature by now.
|

"The natural progress of things is for liberty to yield and government to gain ground." TJ
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
Originally Posted by Big Mac 
Why would they write it to uninstall if it finds Word installed? What sense does that make from the trojan author's perspective?
Some incompatibility.
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Jul 2004
Location: Toronto
Status:
Offline
|
|
Originally Posted by turtle777 
I'd call it bullsh!t.
Yet another anti-virus vendor that attention-whores to get his product / name out.

This story has been running all week at Ars Technica and other tech sites. It's very real.
As for the "who has Java anymore" angle, if you bought your Mac before a year ago and never did a fresh install, you certainly have Java on it. It's was only a year or so ago that Apple removed Java. And lots of people still install it: Minecraft players, OpenOffice users, etc.
And looking at that list of apps, I don't have any of them on my Mac except Xcode and Skype, both of which I could remove since I never use them.
|
|
|
| |
|
|
|
 |
|
 |
|
Professional Poster
Join Date: Sep 2002
Location: New York, NY
Status:
Offline
|
|
Anyone that has Adobe CS has Java. CS requires Java.
|
|
Vandelay Industries
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
|
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
Originally Posted by lpkmckenna 

This story has been running all week at Ars Technica and other tech sites. It's very real.
I'm not calling bullshit on the vulnerability, but on the 550,000 infected Macs number.
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Whatever the number, I can definitely believe it's way more than just a handful. Warez are popular.
Mac users seem to have this weird belief that Mac OS X is immune to malware, and consequently nobody runs anti-viral software.
(
Last edited by Eug; Apr 5, 2012 at 06:13 PM.
)
|
|
|
| |
|
|
|
 |
|
 |
|
Professional Poster
Join Date: Mar 2003
Location: Down by the river
Status:
Offline
|
|
No need to run antivirus just stick with Little Snitch or Hands Off and you're good...plus don't download warez.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
There we go. Mac users seem to have this weird belief that Mac OS X is immune to malware, and consequently nobody runs anti-viral software.
---
In any case, in the very least, running anti-viral software will help prevent Macs from acting as a carrier for Windows malware.
P.S. Apple has re-released the Java fix:
Java developers,
Today we re-shipped our Java 1.6.0_31 for OS X Lion today to address a critical issue we found in Xcode and the Application Loader tool. This new "Java for OS X 2012-002" package is effectively identical to "Java for OS X 2012-001", with the exception of a few symlinks and version numbers.
For the sake of expediency, we have re-rolled the automatic update as our standard full combo updater, with the hope that most users have not yet been presented with 2012-001. We considered creating a delta update for users who already installed 001, but that would have made the process of getting these fixes to you take longer.
We apologize for the inconvenience, and would like to offer our thanks to the developers who caught this issue and reported it to us as quickly as they did. This issue only impacts Lion users, so Snow Leopard users have nothing to reinstall.
Over the next few days, we will catch up with producing updated release notes, tech notes, and developer packages with the revised 002 version numbers.
Manual download links:
Java for OS X 2012-002: <http://support.apple.com/kb/DL1515>
Java for Mac OS X 10.6 Update 7: <http://support.apple.com/kb/DL1516>
(
Last edited by Eug; Apr 6, 2012 at 02:07 AM.
)
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Jul 2004
Location: Toronto
Status:
Offline
|
|
Originally Posted by Eug 
Mac users seem to have this weird belief that Mac OS X is immune to malware, and consequently nobody runs anti-viral software.
I don't run AV software because I don't need to, as Apple includes a striped-down version of ClamAV with OS X anyway. And the presence of trojan horses on the Mac is no reason to run AV, since that would be a false sense of security. New trojan horses are rarely caught by AV software.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Mac users seem to have this weird belief...
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Mar 2001
Location: yes
Status:
Offline
|
|
Originally Posted by lpkmckenna 
I don't run AV software because I don't need to, as Apple includes a striped-down version of ClamAV with OS X anyway.
Your source?
And the presence of trojan horses on the Mac is no reason to run AV, since that would be a false sense of security. New trojan horses are rarely caught by AV software.
And for this? If new trojan horses are rarely caught by AV software, why did it take Apple more than a month to put out the Java update since it was reported? Wouldn't the AV makers be privy to these reports and put out new signatures at least within a month?
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Mar 2001
Location: yes
Status:
Offline
|
|
Two Java updates released within days of one another...
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Yep. One of the criticisms of Mac Security Updates is that Apple takes way too long to issue them. OTOH, the anti-virus software companies issue updates daily.
This two-in-a-row Java update is unusual, but the second one isn't addressing a new security problem. It's just correcting a bug in their previous update.
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Jul 2004
Location: Toronto
Status:
Offline
|
|
Originally Posted by besson3c 
Your source?
Look here, about half way down: Mac OS X 10.7.1 - Source
I'm pretty sure I first heard about this during the last malware scare, which was MacDefender I think.
And for this? If new trojan horses are rarely caught by AV software, why did it take Apple more than a month to put out the Java update since it was reported? Wouldn't the AV makers be privy to these reports and put out new signatures at least within a month?
And yet no AV software agency appears to have issued any updates to catch this recent Java threat, which kinda proves my point.
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Aug 2004
Location: FFM
Status:
Offline
|
|
Originally Posted by lpkmckenna 
I don't run AV software because I don't need to, as Apple includes a striped-down version of ClamAV with OS X anyway.
Only in OS X Server as part of the Mail Server.
|
|
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Apr 2000
Location: Gothenburg, Sweden
Status:
Offline
|
|
Originally Posted by Eug 
Yep. One of the criticisms of Mac Security Updates is that Apple takes way too long to issue them. OTOH, the anti-virus software companies issue updates daily.
Xprotect also updates daily (as required) these days. AFAICT, it does pretty much the same thing as any anti-virus software to protect against a Trojan.
|
|
The new Mac Pro has up to 30 MB of cache inside the processor itself. That's more than the HD in my first Mac. Somehow I'm still running out of space.
|
| |
|
|
|
 |
|
 |
|
Fresh-Faced Recruit
Join Date: Jan 2001
Location: Madison, WI, USA
Status:
Offline
|
|
Now that this has hit every major global wire service and was the top story on the Drudge Report (I guess the millions of other systems infected with malware or part of botnets for years are not very interesting), some thoughts:
Without having a measure of control over the botnet itself, there is no way "Doctor Web" can know how many infected systems there are. Every story has zero confirmation or corroboration of this claim or number beyond from "Doctor Web" or referencing other stories who only use "Doctor Web" as the only source for this claim. They claim, without details, to have used "sinkhole technology" to "count" the number of infected systems. Dr Web's solution? To run their antivirus software, naturally!
Even if Doctor Web managed to become a peer controller on the botnet, it is unlikely they'd be able to tell how many infected systems there actually are. Their current "estimate" may be based on a technique that purports to "predict" how many users are likely to become part of a botnet. IF they have overtaken the botnet's C&C with their "sinkhole technology", then they could stop further infection themselves, as other security vendors have done when they have sinkholed botnet C&C servers.
Interesting, no? Malware absolutely exists for Mac OS X, but there is no independent evidence I can see at present that Flashback is any worse than any previous Mac malware. Bravo to Doctor Web for becoming the latest security company to learn that "Apple" is the quickest way to rocket to the forefront of not only the IT press, but all media.
My issue is that I don't even think it's "600,000" for the reasons I outlined above. Either it's an estimate backed in no way by actual numbers, or they have overtaken part of the botnet's command and control. And security vendors have indeed done this before, but they do it to STOP the botnet, not to count infected hosts as a PR stunt and hawk their wares. So either way, "Doctor Web" — first time I have ever heard of them, by the way, in two decades in enterprise IT — and their claims are suspect.
My comments should not be construed to mean there are no security or malware threats to Mac OS X. There are. Many. Apple, which currently manages the Java distribution on Mac OS X, also left the Java exploit described in CVE-2012-0507 unpatched for weeks. To the extent that stories like this may remind Mac users to not be complacent, it's positive. Unfortunately, from an IT impact perspective, there are far greater threats, significantly larger botnets, and much more severe consequences.
|
|
|
| |
|
|
|
 |
|
 |
|
Administrator  Join Date: Mar 2000
Location: Land of the Easily Amused
Status:
Offline
|
|
I'm with turtle on this. I really doubt the half million+ numbers being bandied about. Does anyone here know of a single person infected?
Anyone?
|
|
|
| |
|
|
|
 |
|
 |
|
Fresh-Faced Recruit
Join Date: Jan 2001
Location: Madison, WI, USA
Status:
Offline
|
|
Originally Posted by Demonhood 
I'm with turtle on this. I really doubt the half million+ numbers being bandied about. Does anyone here know of a single person infected?
Anyone?
Yes...I have a couple of colleagues who have found infected systems — but that is across literally hundreds of thousands of Macs at government and academic sites. Our site alone has over 25,000 Macs and I have yet to see an infection.
Flashback is real, but the "600,000" claim, and the way Doctor Web made the claim, is suspect (see my prior message). Throwing that number out is the only way they got the publicity they did, and why this story has taken off in the press.
|
|
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Jun 2000
Location: inside 128, north of 90
Status:
Offline
|
|
With all the "free game" crap my dad downloads, I hope he is free of this. At least he has skype installed and I've sent him instructions for updating java...
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Jul 2004
Location: Toronto
Status:
Offline
|
|
Ars: Half-million Mac infection estimate backed by new analysis.
Is anyone still skeptical about those numbers?
I was very interested in this paragraph:
Soumenkov said Flashback is distributed on compromised websites as a Java applet that's disguised as an update for the Adobe Flash Player. "The Java applet then executes the first stage downloader that subsequently downloads and installs the main component of the Trojan," he wrote. "The main component is a Trojan-Downloader that continuously connects to one of its command-and control (C&C) servers and waits for new components to download and execute."
I never, never click on update requests for Flash for this very reason. Abode changes the look of the update alert so often that I can never trust that the update message is actually from them.
So then I have to go to the Flash Pref Panel (a relatively recent addition to Flash), click update, which doesn't actually do an update (like every single other Pref Panel does), but instead goes to a link on Abobe's website. And I have to read the version number from the Panel and compare it to the version number on the website, then download and install.
Update Perian? Open Pref Panel, click update, done.
Update Windows Media? Open Pref Panel, click update, done.
Abode are a bunch of fncking incompetent twits.
Remember when Jobs got on stage and hammered Java and Flash for being instability and security nightmares?
And there are still people who want to see Flash or Java on iOS?
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Nov 1999
Location: 888500128, C3, 2nd soft.
Status:
Offline
|
|
Originally Posted by lpkmckenna 
Update Perian? Open Pref Panel, click update, done.
Update Windows Media? Open Pref Panel, click update, done.
Abode are a bunch of fncking incompetent twits.
Remember when Jobs got on stage and hammered Java and Flash for being instability and security nightmares?
And there are still people who want to see Flash or Java on iOS?
Social engineering can't really be blamed on Adobe here.
I got this exact pop-up a few weeks ago, btw. I do not have Java enabled in Safari, and my machine did not get infected.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
Originally Posted by lpkmckenna 
So they just registered a domain that the Trojan would use as a fall back ?
Weird, you'd think whoever programmed the Trojan would make sure his domains are under his control.
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Impressive.
"In less than 24 hours, a total of 600,000 unique bots connected to their server."
So, the number is actually higher than the estimate nobody believed. (Of the unique bots, they estimate 98% are from Macs.)
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Oct 2001
Location: Automatic
Status:
Offline
|
|
We should start a poll on this one. Clean or infected ?
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Well, whaddya know. I did full system scans, and I had this on a machine. Sophos didn't prevent the infection because it wasn't added to their database until April 6... which is the same time Apple issued the patch I think.
|
|
|
| |
|
|
|
 |
|
 |
|
Ham Sandwich
|
|
Wow... of all the applications, I had Skype.
Give me a break. Why would these dorks program a trojan that would terminate if I had, of all things, once-in-a-while Skype on my Mac?
That just sounds like a stupid-ass trojan.
Now let's get the article for the name/arrest of the SOB(s) who started this mess.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
P.S. There is no security update for my G4 Macs running 10.5, but I have Sophos running on those too.
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Oct 2001
Location: Automatic
Status:
Offline
|
|
Well, whaddya know. I did full system scans, and I had this on a machine. Sophos didn't prevent the infection because it wasn't added to their database until April 6... which is the same time Apple issued the patch I think.
So it is useless, whereas Intego's VirusBarrier X6 would have protected your Mac. Is there any free option worth a dime.? I use both, Intego's and ClamXav, but my systems are clean so I don't know how efficient ClamXav would be.
Also, Microsoft needs to bring Office to the Mac App Store ASAP. I mean, 600,000 Macs with no Office is insulting.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Originally Posted by angelmb 
So it is useless, whereas Intego's VirusBarrier X6 would have protected your Mac. Is there any free option worth a dime.? I use both, Intego's and ClamXav, but my systems are clean so I don't know how efficient ClamXav would be.
Intego would likely be better given its more robust feature set, but Sophos free is better than not running anything.
|
|
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Aug 2001
Location: Nobletucky
Status:
Offline
|
|
Reading the ClamXav forums, it sounds like they've been updating their definitions as fast as they are made aware of a new Flashback variant. And there are a surprisingly large number of variants...at least 60. They also seem to to think Skype can be an attack vector.
|
|
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Apr 2000
Location: Gothenburg, Sweden
Status:
Offline
|
|
Originally Posted by Eug 
P.S. There is no security update for my G4 Macs running 10.5, but I have Sophos running on those too.
I think the vulnerability in question requires Java 6, which does not run on G4s at all.
|
|
The new Mac Pro has up to 30 MB of cache inside the processor itself. That's more than the HD in my first Mac. Somehow I'm still running out of space.
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Sep 2000
Location: Isle of Manhattan
Status:
Offline
|
|
I think the question still stands - has anyone actually seen this thing?
Network Security people are have orgasms over the thought of Macs being infected, and relish the fear factor they now have in their hands. I call the whole thing baloney (the mass infection, not the possible exploit).
(
Last edited by osiris; Apr 10, 2012 at 09:51 AM.
)
|
|
"Faster, faster! 'Till the thrill of speed overcomes the fear of death." - HST
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Aug 2001
Location: Nobletucky
Status:
Offline
|
|
The IT department at the university my daughter attends is taking this seriously enough to send out an email yesterday alerting Mac users to the problem and directing them to information on how to deal with it.
Ironically, it came at the same time as their Google-based webmail system is being hit hard by some bot/virus sending multiple empty PDFs to every email address in their sent mail folder.
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Sep 2000
Location: Isle of Manhattan
Status:
Offline
|
|
Originally Posted by Thorzdad 
The IT department at the university my daughter attends is taking this seriously enough to send out an email yesterday alerting Mac users to the problem and directing them to information on how to deal with it.
Ironically, it came at the same time as their Google-based webmail system is being hit hard by some bot/virus sending multiple empty PDFs to every email address in their sent mail folder.
Sure, IT is taking it seriously, but is it real?
|
|
"Faster, faster! 'Till the thrill of speed overcomes the fear of death." - HST
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Jun 2001
Location: planning a comeback !
Status:
Offline
|
|
My mom's MBP did NOT have the trojan on it.
I concluded that there is NO WAY that this threat is REAL.
-t
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Originally Posted by osiris 
I think the question still stands - has anyone actually seen this thing?
Network Security people are have orgasms over the thought of Macs being infected, and relish the fear factor they now have in their hands. I call the whole thing baloney (the mass infection, not the possible exploit).
Did you miss my post above? One of my Macs was infected, and I even run anti-virus software full-time. (The Sophos virus definitions update that included Flashback only came out April 6 though, so it must have gotten infected before that.)
---
Flashback Checker
FlashbackChecker runs the tests described in the F-Secure Bulletin as of April 6th, 2012.
Note This utility checks and reports the presence of Flashback malware, it does not remove it!
Worried about Mac malware? Just set up OpenDNS.
OpenDNS — security and DNS provider of choice for 2% of all Internet users — is blocking the Flashback Trojan, or what’s being described as one of the single biggest Mac security incidents of all time. As OpenDNS does in cases of very large scale attacks like this, the protection is included in Premium DNS and completely free to users.
(I use a combination of OpenDNS and Google's DNS servers.)
Apple Snubs Firm That Discovered Mac Botnet, Tries To Cut Off Its Server Monitoring Infections
Boris Sharov, chief executive of the Moscow-based security Dr. Web says he learned Monday from the Russian Web registrar Reggi.ru that Apple had requested the registrar shut down one of its domains, which Apple said was being used as a “command and control” server for the hundreds of thousands of PCs infected with Flashback. In fact, that domain was one of three that Dr. Web has been using as a spoofed command and control server–what researchers call a “sinkhole”–to monitor the collection of hijacked machines and try to understand their behavior, the technique which allowed the firm to first report the size of Apple’s botnet last week.
“They told the registrar this [domain] is involved in a malicious scheme. Which would be true if we weren’t the ones controlling it and not doing any harm to users,” says Sharov. “This seems to mean that Apple is not considering our work as a help. It’s just annoying them.”
Sharov believes that Apple’s attempt to shut down its monitoring server was an honest mistake. But it’s a symptom of the company’s typically tight-lipped attitude. In fact, Sharov says that since Dr. Web first contacted Apple to share its findings about the unprecedented Mac-based botnet, it hasn’t received a response. “We’ve given them all the data we have,” he says. “We’ve heard nothing from them until this.”
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Sep 2000
Location: Isle of Manhattan
Status:
Offline
|
|
Sorry, I did miss your post there.
Was it active and doing what is was supposed to be doing?
Or was it as if a PC friend emailed you an infected Word Doc and it just happened to be on your machine?
|
|
"Faster, faster! 'Till the thrill of speed overcomes the fear of death." - HST
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Originally Posted by osiris 
Sorry, I did miss your post there.
Was it active and doing what is was supposed to be doing?
Or was it as if a PC friend emailed you an infected Word Doc and it just happened to be on your machine?
It was in my user directory IIRC. I don't know if it was doing anything: If I've already been infected, and I apply that Apple Security Update, is it able to do anything? Cuz by the time I found it, I had already applied the security update. However, it had to have been there before the security update. I guess I should change all my web passwords now.
BTW, I don't think Word docs can be infected with this.
|
|
|
| |
|
|
|
 |
|
 |
|
Addicted to MacNN
Join Date: Sep 2000
Location: Isle of Manhattan
Status:
Offline
|
|
Originally Posted by Eug 
BTW, I don't think Word docs can be infected with this.
I was implying that an infected file from a PC would do you no harm, so my hope was that this new Java thing was behaving the same way - not doing anything.
edit: by all means, change your passwords, including your admin account.
|
|
"Faster, faster! 'Till the thrill of speed overcomes the fear of death." - HST
|
| |
|
|
|
 |
|
 |
|
Dedicated MacNNer
Join Date: Jun 2006
Location: Chicago
Status:
Offline
|
|
Originally Posted by Eug 
It was in my user directory IIRC. I don't know if it was doing anything: If I've already been infected, and I apply that Apple Security Update, is it able to do anything? Cuz by the time I found it, I had already applied the security update. However, it had to have been there before the security update. I guess I should change all my web passwords now.
BTW, I don't think Word docs can be infected with this.
Applying the update does not remove it...you have to remove it yourself.
|
|
|
| |
|
|
|
 |
|
 |
|
Clinically Insane
Join Date: Dec 2000
Location: Caught in a web of deceit.
Status:
Offline
|
|
Originally Posted by osiris 
I was implying that an infected file from a PC would do you no harm, so my hope was that this new Java thing was behaving the same way - not doing anything.
It was not encased in a zip file or in another file or anything.
Originally Posted by QSilver 
Applying the update does not remove it...you have to remove it yourself.
I know applying the update doesn't remove it. However, I was wondering if applying the update could block it.
|
|
|
| |
|
|
|
 |
|
 |
|
Moderator  Join Date: Apr 2000
Location: Gothenburg, Sweden
Status:
Offline
|
|
No, it does not block it. Once it manages to execute once, it only ever uses legitimate methods.
|
|
The new Mac Pro has up to 30 MB of cache inside the processor itself. That's more than the HD in my first Mac. Somehow I'm still running out of space.
|
| |
|
|
|
 |
 |
|
 |
|
|
|
|
|
 
|
|
 |
Forum Rules
|
 |
 |
|
You may not post new threads
You may not post replies
You may not post attachments
You may not edit your posts
|
HTML code is Off
|
|
|
|
|
|
 |
 |
 |
 |
|
 |